Game hosting perfected,that's Physgun
Physgun powers all the big guys, and we're ready to power you too. We've built a platform with features and performance you won't find anywhere else period.
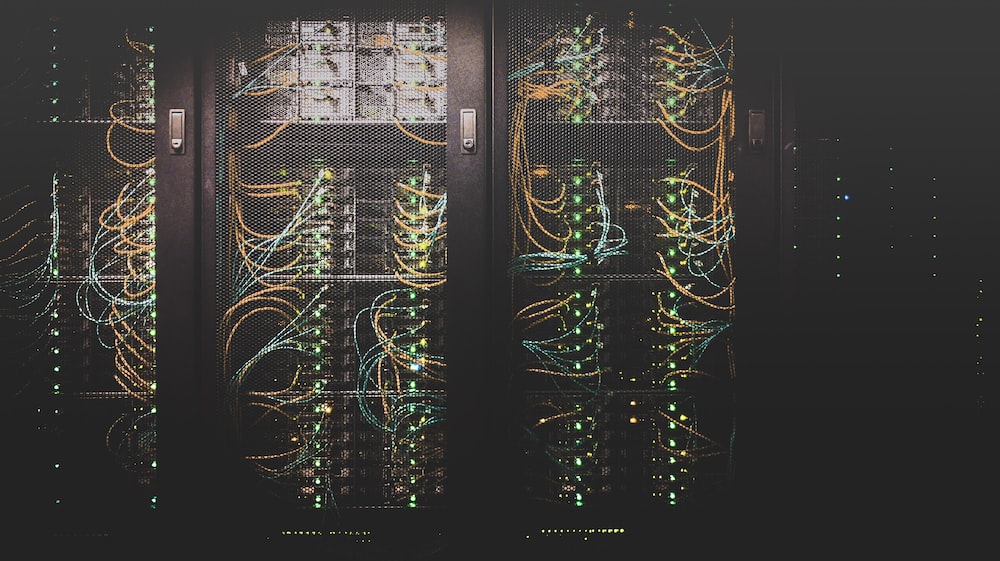
High Performance Game Server Hosting
Physgun was built from the ground up to support high player counts for the most demanding games. Below, you can find our most popular offerings.
Features
Let us show you what makes Physgun #1
Overwatch
Crush exploiters and malicious traffic with our state of the art network protection and game specific protection. Gone is the fear of being taken offline due to a bad actor, focus on building your community.
Optimizations
Our panel comes with free engine-level optimizations, keep your network usage low, and your cpu stable. Everyone hates crashes, and if you do crash, our custom crash handler will either recover your server, or tell you exactly what happened.
All your favorite addons, in one place
When choosing Physgun as your host, you'll get unlimited access to premium addons for free from creators like Billy, Srlion, and other Gmodstore creators
Our engine-level crash recovery and detection is a trail blazer in the industry, completely unique to Physgun
Physgun has multiple source engine specific optimizations not seen in any other competitor
No other competitor features free premium addons like Physgun, worth hundreds in value!
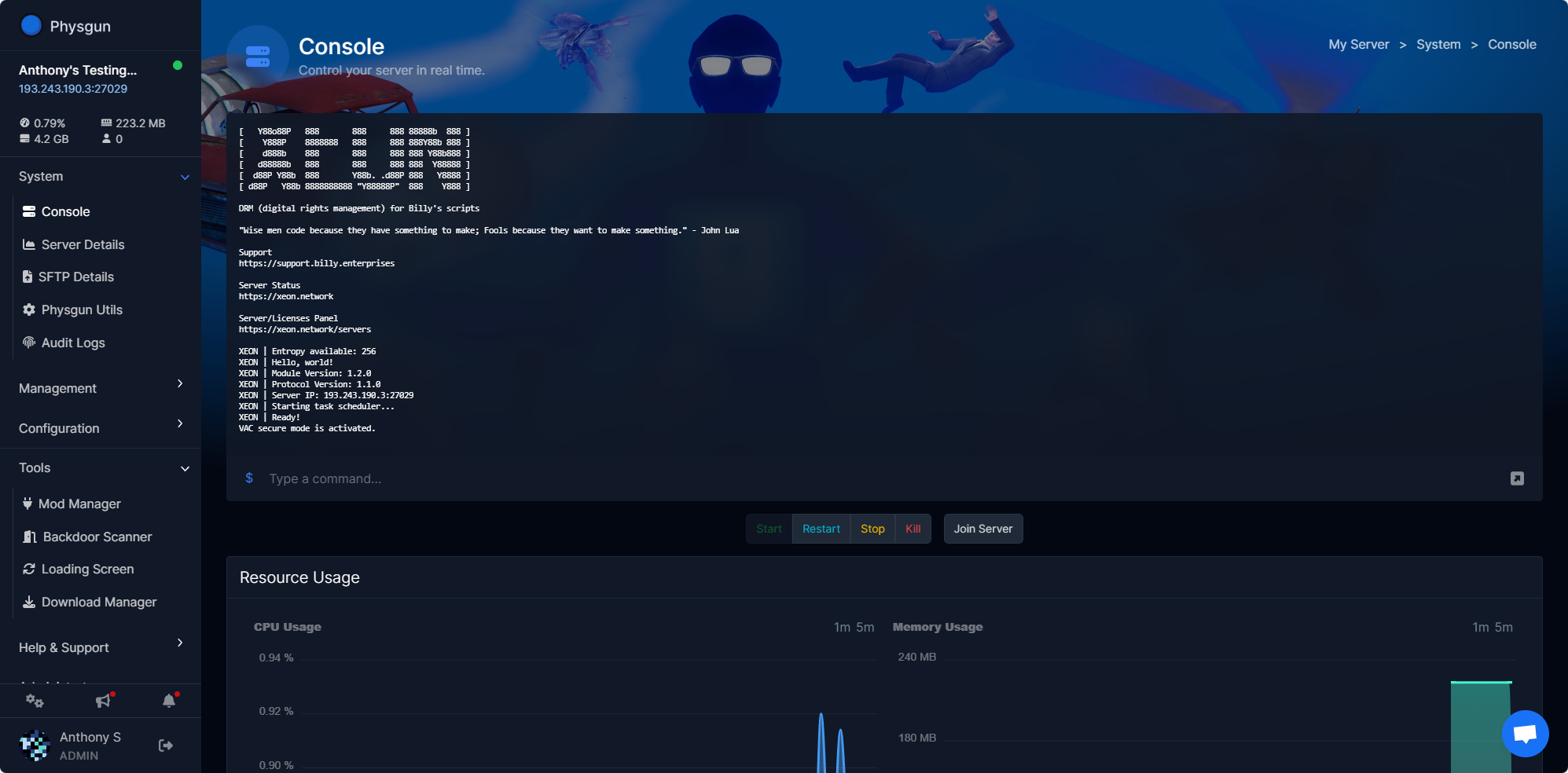
Physgun Panel
A game panel built from the ground up to make your life easy.
Simple, and Affordable Prices for all.
Physgun provides the best value in game hosting period. Everything you need to run a successful server is included in our pricing.
With another provider? Chat with us on Discord, discounts available.
All services include a free transfer from your current provider.
Garry's Mod
Physgun Suite (AntiExploit and more)
Overclocked Ryzen 9 7900X
DDR5 Memory
NVMe Storage
MySQL Database
US Chicago or UK London
Leading DDoS Protection & Anycast
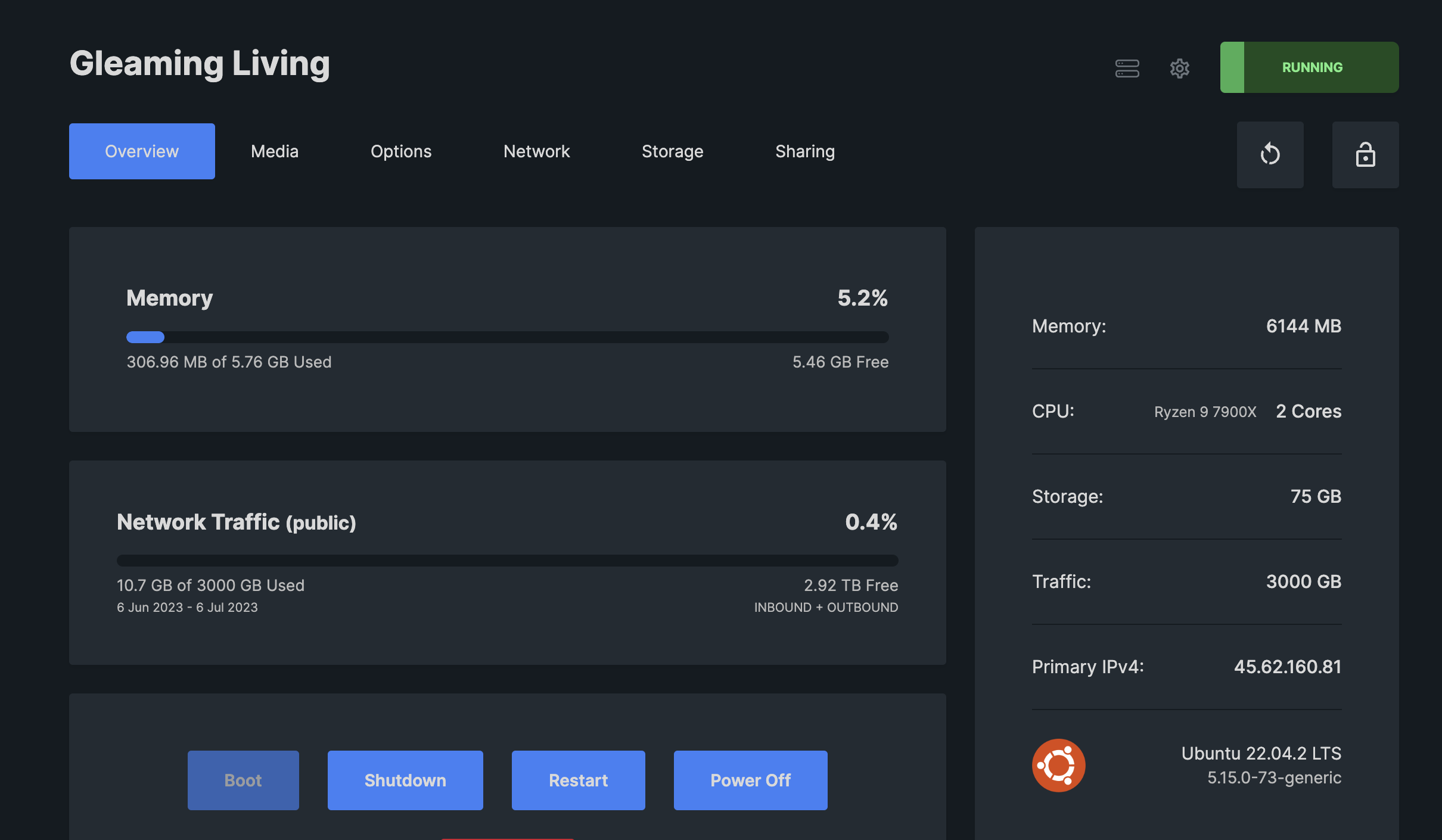
VPS Hosting
Firewall & Filter Manager
Ryzen 9 7900X
DDR5 Memory
NVMe Storage
Easy OS Installation
US Chicago
Leading DDoS Protection & Anycast

Rust
uMod/Carbon/Oxide
Overclocked Ryzen 9 7900X
DDR5 Memory
NVMe Storage
MySQL Database
US Chicago or UK London
Leading DDoS Protection & Anycast

Palworld
Easy Configurator
Overclocked Ryzen 9 7900X
DDR5 Memory
NVMe Storage
MySQL Database
US Chicago or UK London
Leading DDoS Protection & Anycast

Minecraft
Vanilla, Spigot, Paper, or Forge
Ryzen 9 / Ryzen 7 / Intel Xeon V3
DDR4 Memory
NVMe Storage
MySQL Database
US Chicago or UK London
Leading DDoS Protection & Anycast
Unturned
Rocketmode, Openmod, or Vanilla
Overclocked Ryzen 9 7900X
DDR5 Memory
NVMe Storage
MySQL Database
US Chicago or UK London
Leading DDoS Protection & Anycast

Team Fotress 2
SourceMod & MetaMod
Overclocked Ryzen 9 7900X
DDR5 Memory
NVMe Storage
MySQL Database
US Chicago or UK London
Leading DDoS Protection & Anycast

Dedicated
Hardware Perfect For You
99% Uptime
Reliable & Redundant Network
Enterprise or Gaming Solutions
Fast & Reliable Support
Colocation Available
Leading DDoS Protection & Anycast
Website
cPanel Included
Xeon E3
Redundant Storage
Supports Prometheus, Cosmo, and more
Easy to use
US Chicago
Leading DDoS Protection & Anycast
Still on edge? Join our discord!
Ask all your questions. We are ready to get you setup with the best game hosting solution.
Join Discord

